SECURE IoT NETWORK
Data processing, storage and communication from vulnerable connected object to server increases the risk of data forgery, inaccurate information or fraudulent transactions. Internet-of-thing device securisation is imperative as long as data is valuable for businesses. Trust IoT enables chip-to-server secure data transmission and object secure authentication. Trust IoT securely connects the IoT devices to server or cloud services. Integrate Trust IoT chip to your connected devices to get in a single command : secure authentication, data encryption and transaction uniqueness.
TRUST IoT

AUTHENTICATE CONNECTED OBJECT
OPTIONNAL RF-INTERFACE
ENROL DEVICE SECURELY
TRUST COLLECTED DATA
EASY-TO-INTEGRATE
ALL-IN-1-COMMAND
OBJECT AUTHENTICATION
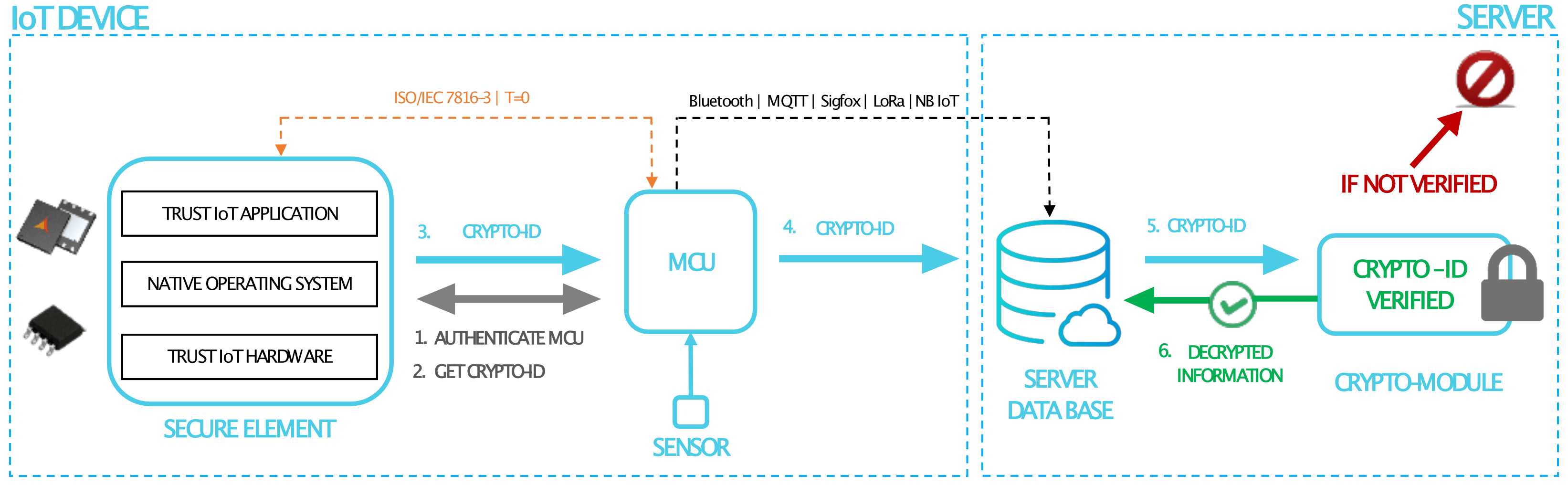
Trust IoT authenticates MCU and generates encrypted, unique and unreplicable CRYPTO-ID
Secure connection with proof of origin is made between authenticated device and clouds/servers
FIELD DATA PROTECTION
Trust IoT permits to transmit up to 128 bytes of collected data (protected by MAC or MAC + encryption)
Data from MCU can be transmitted to secure element in a secure session
OPTIONAL RF INTERFACE
Trust IoT comply with ISO/IEC 14443-A standard
Data can consequently be collected directly on the field with an authorized NFC-device (External authenticate or CHV)
HOW TRUST IoT WORKS?
MAIN ADVANTAGES
- Identify connected objects on the field and trust collected Data
- Secure authentication & Data encryption in one command
- Easy to integrate with internet-of-things devices
- End-to-End Security, from chip to server
- Direct interaction with RF-interface
SECURITY FEATURES
- MCU access condition with CHV verification or External authenticate
- Up to Common Criteria EAL5+ hardware certification
- AES-128 cryptography for authentication/encryption
- Key storage & management with MSE
- Dynamically computed CRYPTO-ID
USE CASES
INDOOR LOCATION
BLE BEACONS and ZIGBEE allow to locate assets indoor. It reduces lost, thefts and time waste.
Trust IoT authenticates and identifies devices to ensure a trustable and accurate information.
RFID Interface permits to easily register and identify object on the field.
SMART GRID
Smart meters permits to monitor electricity-consumption and to make a billing based on data.
Trust IoT allows energy provider to secure electricity-use records as well as revenues.
PERIMETER ACCESS CONTROL
Connected devices ensure detection of people in non-authorized or restricted access area.
Trust IoT ensures a non-jeopardized information and all intrusion detection will be communicated.
SUPPLY CHAIN CONTROL
Smart meters allows to monitor the storage conditions in metering humidity, temperature or light.
With its contactless interface, Trust IoT permits to collect data directly on the field with a NFC devices.
In this way, managers are able to monitor temperature or humidity, even when connectivity is not ensured.
FLEET TRACKING
eUICC & GPS open new possibilities in terms of fleet tracking, routes prediction and logistics tracing. Trust IoT authenticates and identifies devices to a make sure the correct vehicle is tracked.
FALL DECTECTION
BLE BEACONS equipped with accelerometer helps to be aware and prevents fall.
This technology helps elderly, disable or hospitalized people living independent.
Trust IoT allows to easily collect identifier through RF-interface and register on phone application.
PATIENT SURVEILLANCE
Captors and sensors permit to monitor the vital signs (Body temperature, Pulse rate, Blood pressure, etc.).
Trust IoT protects privacy and keeps patient information confidential.
IP CAMERAS
Remotely connected cameras allows to receive image in real time without complex installations.
Trust IoT protects privacy and ensures video images come from authenticated & trusted camera.
